
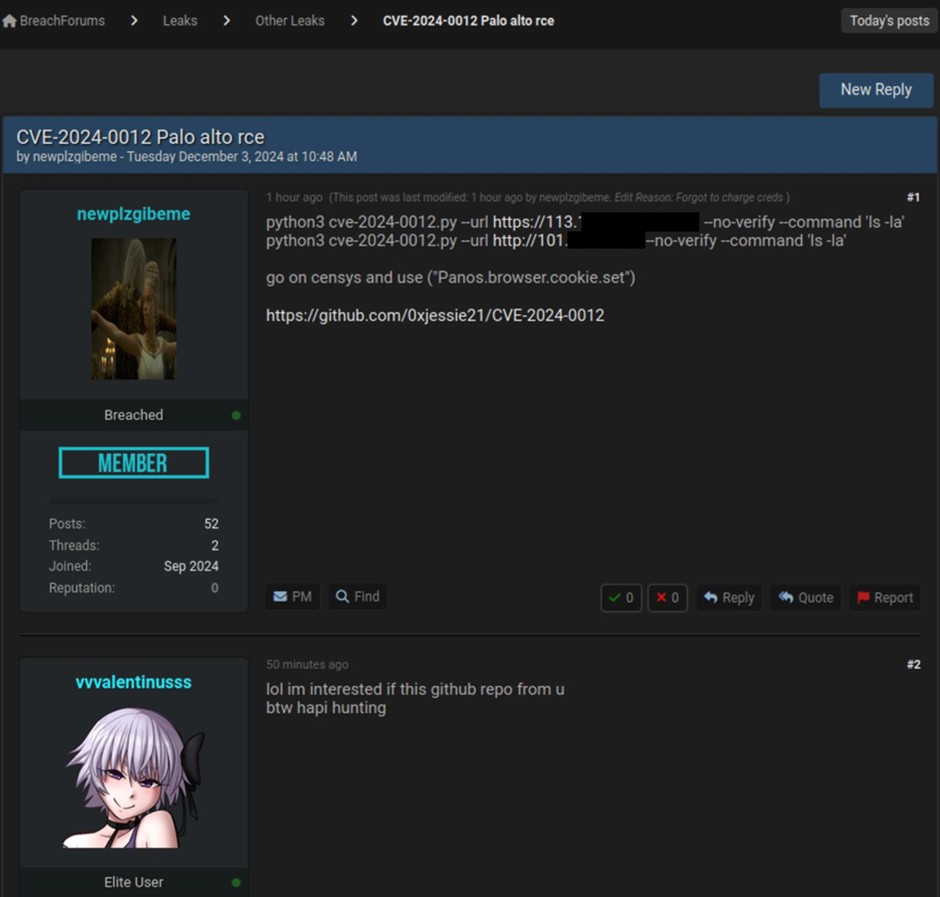
A few hours ago on Breach Forum, a threat actor by the name “newplzqibeme” shared a GitHub repository where a python-written exploit for active exploitation of CVE-2024-0012 on PanOS (the Palo Alto firewall operating system) is published.
The exploit grants the attacker, full administrative access to the firewall with an Authentication Bypass mechanism, gaining administrator access.
The post by “newplzqibeme” shows two public IPs as examples, which are most likely exposed and vulnerable firewalls.
Firewalls running PanOS 10.2, 11.0, 11.1 and 11.2 are affected by this CVE if not upgraded to the respective versions (>= 10.2.12-h2, >= 11.0.6-h1, >= 11.1.5-h1 and >= 11.2.4-h1).
The CVE, categorized with level 9.3 (still under review), allows precisely full administrative access to the firewall and the exploit tool publicly available on GitHUB, also allows the creation of a Reverse Shell for the attacker. The script on GitHUB is up to date (last updated December 1, 2024).
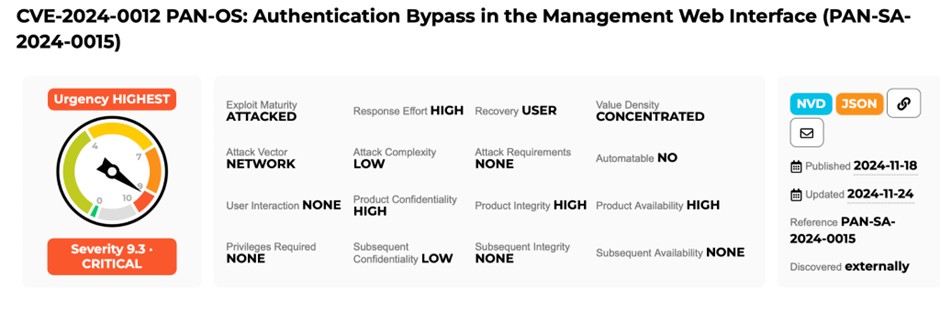
Palo Alto’s site has all the information about the CVE, possible mitigations, and technical details.
Palo Alto’s site also mentions a POC (Proof Of Concept) for exploiting such a CVE that we found on GitHUB (also relatively up-to-date as of 15 days from the writing of this article).
Our advice is to take immediate action on any firewalls exposed on the Internet with the administration web interface, and more! Even unexposed firewalls may are vulnerable to such an attack if access is from a trusted network; in the unfortunate event that a thread actor already has access to your networks.
Right now there are about 257 thousand exposed devices on the Internet that respond to Palo Alto Global Protect. You should update these devices, if you have them, to prevent unwanted access by attackers
