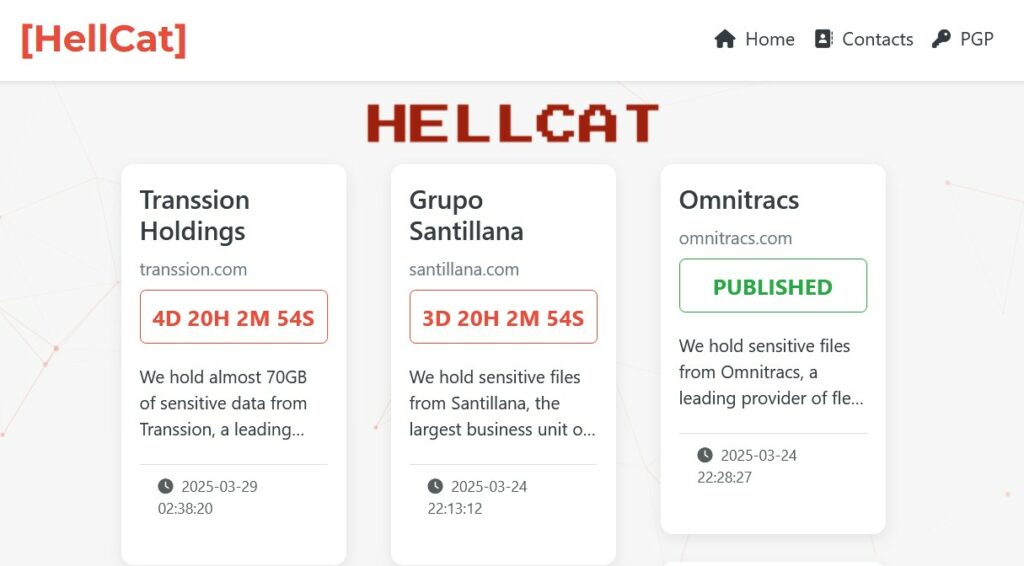
HellCat ransomware appeared in the second half of 2024 with and it has attracted the attentions of analysts thanks to the humor within their public statements. We recall the attack to Schneider Electric in France where the group ended up to request a “baguette payment” in their DLS.
HellCat group targets are high profile organizations (like Orange, Telefónica, Zurich Group and Pinger) with prolific TTPs which include Jira ticketing system abuses and exploitation of vulnerable public interfaces. One of their recent victims is Jaguar Land Rover that led to a data breach wich highlighted the risk when relying on legacy credentials.
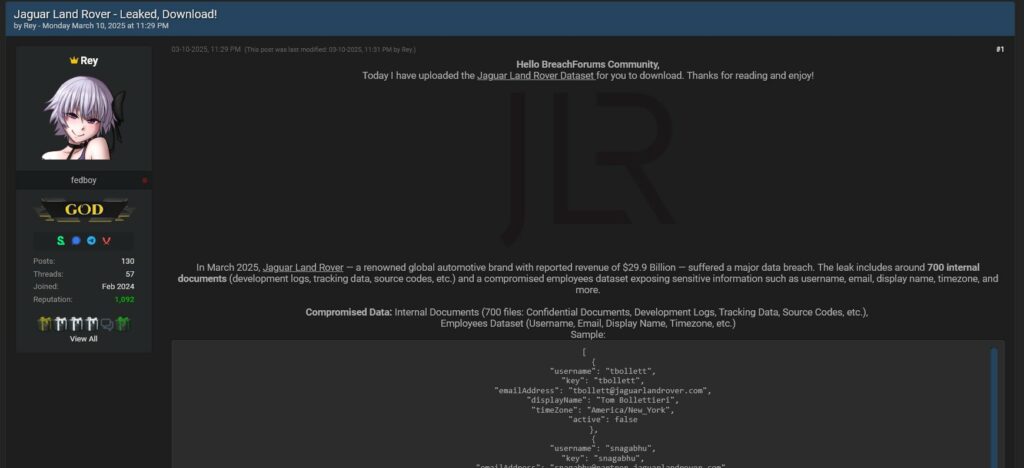
HellCat decided to evolve further starting to develop their own affiliate program making the group a de-facto Ransomware-as-a-Service provider. This choices could leverage HellCat ransomware making it more popular than it has been in the last months, this is why we wanted to reached out the group to ask some questions about their new RaaS program and how they plan the future of HellCat. Take this opportunity to get in touch directly with a new player in the ransomware ecosystem and understand some insight directly from the source. Currently, the HellCat affiliate program is under development, and one of the admins, Rey, shared some early spoilers by also showing a screenshot of the new ransomwware called HellCat 2.0.
We take the opportunity to thank again for their openness and availability to share their words with our readers.
RHC: HellCat, thank you for agreeing to be a guest on RedHotCyber! Before we begin, we give you a chance to introduce yourself to our readers. What is it and how did HellCat come about?
HellCat: It all started with a small hacking grouporiginally conceived as a modest collective within the community. We never intended to create something overly complex or advanced at first. However, after establishing our foundation and achieving some early successes, I decided to elevate our efforts into a refined brandone I had envisioned for a long time but never had the opportunity to fully realize. Today, HellCat is focused on high-profile targets, a strategic choice that underscores our ambition and specialized expertise.
RHC: Until now HellCat did not have an affiliate program. What prompted you to become a RaaS? What services and benefits do your affiliates have once they become affiliates? Do you have any rules about ransomware use andor victim selection? Why choose HellCat over the competition?
HellCat: We never officially announced any intention to transition into a Ransomware-as-a-Service RaaS model however, the media labeling us as such prompted me to consider developing an affiliate program to address these misconceptions. Our affiliates benefit from a state-of-the-art locker that incorporates all the modern features found in todays ransomware toolsits advanced, affordable, and designed for maximum efficiency. We enforce strict rules even within our affiliate program, we target only high-profile victims and never engage in low-profile attacks. For instance, we require that targets generate a minimum annual revenue of 40 million. Additionally, HellCat offers the most competitive ransom payment splits on the market, ensuring that our partners are well-compensated while upholding our own ethical guidelines.
RHC: Tell us about your ransomware family, what platforms do you support and what features are there besides data encryption? What languages do you use during development and how do you program potential enhancements? Have you taken cues from other ransomware in the landscape
HellCat: While I cant disclose all the details, our ransomware family boasts a comprehensive set of features that rival those found in the most renowned tools on the market. It is engineered to be versatile and robust, supporting multiple platforms to maximize reach and efficiency.
RHC: Do you plan to develop additional tools beyond ransomware to offer your affiliates?
HellCat: Yes, we are currently developing several additional tools to complement our ransomware platform. These enhancements are designed to provide our affiliates with more comprehensive capabilities and improve overall effectiveness.
RHC: How would you convince a potential affiliate to join your new RaaS?
HellCat: I believe the strength of our offering speaks for itself. We market our services effectively because we understand exactly what our affiliates are looking for.
RHC: Can you reveal the size of your group outside the affiliates? Since the founding of HellCat, have you enlisted new members? Do you have any requirements to be part of the HellCat team outside the affiliates? Do you have past experience with other groups outside of HellCat?
HellCat: Since HellCats inception, we have welcomed at least four new members to our core team. However, we remain highly selective about who joins usthere are specific requirements and a rigorous vetting process in place. My previous experiences with other groups have underscored the importance of maintaining high standards and ensuring that every member aligns with our overall strategy and ethical considerations.
RHC: On average, what is the security level of the victims? What would you advise organizations out there to avoid being impacted by groups like yours?
HellCat: Frankly, the average security level of our victims is quite low. My advice to organizations is to invest in comprehensive employee training and ensure that everyone understands the basics of cybersecurity. Most attacks succeed because of social engineering tactics, so fostering a strong culture of security awareness is crucial. Regular software updates, strong password policies, and ongoing training can significantly reduce the risk of falling victim to such attacks.
RHC: Do you have any areas that you prioritize? If yes, which ones and why?
HellCat: Our strategy is straightforward we target victims based solely on their value. We do not discriminate by industry or geographical location, as long as the victim represents a high-profile case with significant financial resources. This approach allows us to maximize our impact while maintaining a consistent operational standard.
RHC: What do you expecthope from this transition from a closed group to RaaS? Do you have any goals you want to achieve? Have you given yourself a time or financial limit, or do you plan to continue your activity indefinitely?
HellCat: My primary goal is to expand the HellCat name and reputation. Financial gains are reinvested into further development. As long as I have the means to keep innovating and the drive to push forward, I dont see this as a temporary phaseour operations are designed to continue indefinitely.
RHC: Do you have a message for future potential victims that you want to make public?
HellCat: We do not issue direct messages. The reality is simple victims will soon face the consequences of failing to secure their systems. Its not personalthis is simply the nature of our operations. If you are unprepared or neglect basic security measures, you will inevitably pay the price.
RHC: Your group appeared in 2024, how would you judge this period? What were the difficulties in the creation and continuation of HellCat? Plans for the future?
HellCat: Looking back, the journey has been quite smooth despite occasional periods of inactivity. We have executed numerous successful attacks, including operations we didnt disclosesuch as backdooring BitGos software, compromising China Life Insurance, and breaching Telefonica. These operations were challenging yet exhilarating, reaffirming our commitment and capability. We have many plans in the pipeline, and our focus remains on growth and continuous innovation.
RHC: After your attack on Schneider Electric you demanded payment in baguettes, is this a new method of evading money laundering controls? What makes baguettes a better currency than Bitcoin or Monero? Did you have plans to resell baguettes by creating a new monetization method? How did Schneider Electric respond to your request?
HellCat: When we demanded payment in baguettes, it wasnt a reference to any cryptocurrencywe literally meant bread. It was a tongue-in-cheek way to mock the corporate roots of the French company Schneider Electric. We never expected a conventional response the gesture was purely satirical. To add another layer of irony, we even facilitated the registration of a company in France under the name HELLCAT SOFTWARES RAAS. You can see proof here https://annuaire-entreprises.data.gouv.frentreprisejoannie-leclerc-hellcat-raas-softwares-532279932.
RHC: HellCat, thank you again for your time and for your very valuable responses to our readers! We leave this last space for you to say what you want in total freedom.
HellCat: Thank you for the opportunity to share our perspective. I look forward to witnessing how our operations evolve and further strengthening the HellCat brand. The journey ahead is filled with innovation and continuous growth, and I am confident that our approach will not only redefine industry standards but also challenge the status quo. Take care.
Follow us on Google News to receive daily updates on cybersecurity. Contact us if you would like to report news, insights or content for publication.