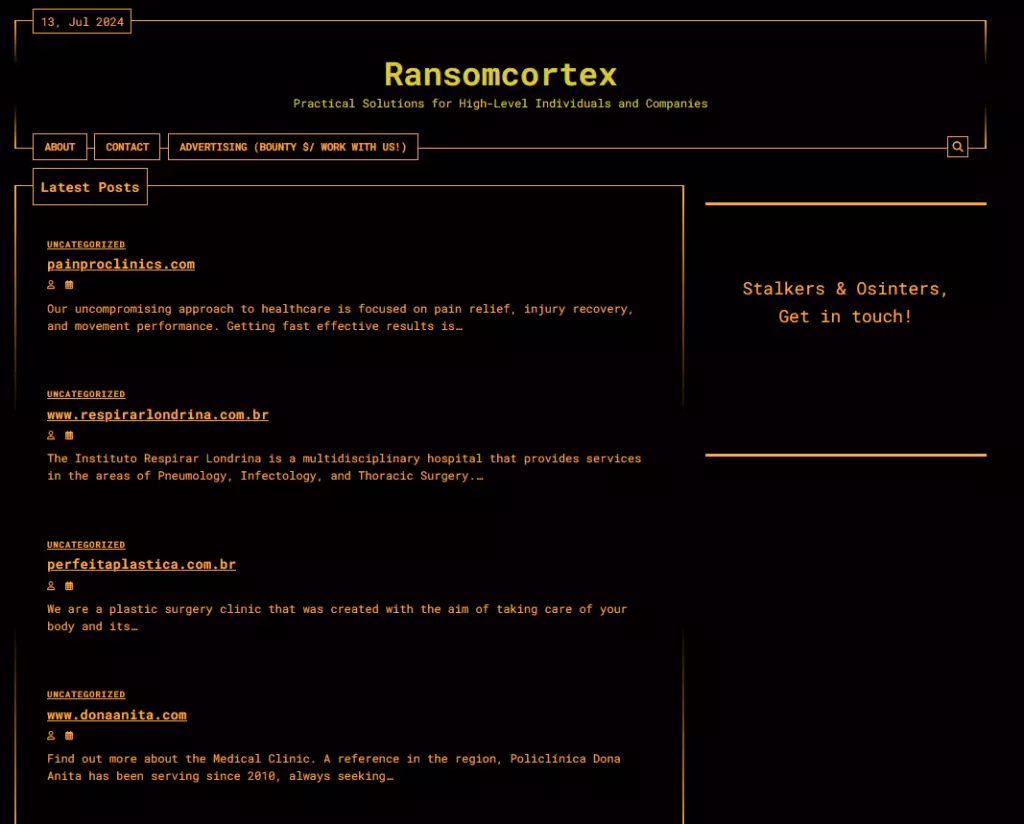
Ransomcortex is a new cyber ransomware gang that resonates menacingly in the healthcare sector.
This group has quickly attracted attention for its specialization in attacks on healthcare facilities, striking four institutions in a matter of days, including three in Brazil and one in Canada. This group demonstrated extraordinary efficiency and a clear “on target” strategy, highlighting the vulnerability of a sector already under tremendous pressure.
Ransomcortex’s targeted focus on healthcare organizations raises crucial questions: why this sector and what are the real targets of these criminals? Extremely sensitive and valuable health information is a tempting target for financial fraud, extortion, and black market sales.
Ransomware attacks against hospitals and clinics are not only a cybersecurity issue, but also a public safety issue, with direct implications on patients’ lives. For this reason, they should be considered critical national infrastructure and properly protected.
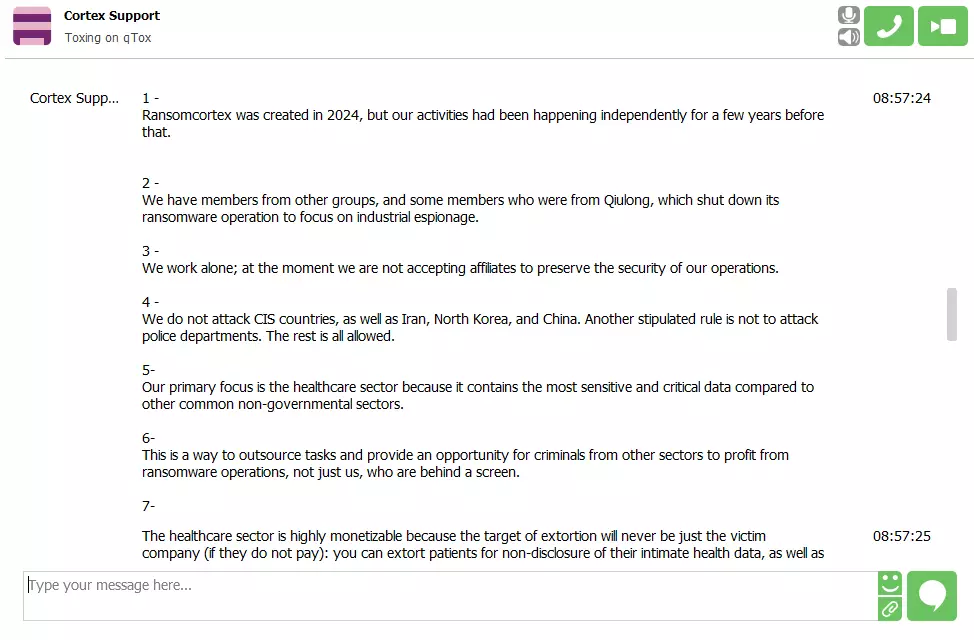
To better understand the motivations and methodologies of Ransomcortex, we obtained an exclusive interview with members of the group. This conversation offers a rare window into the inner workings of a cyber gang that has chosen to target one of the most critical sectors of our society. We will discuss their operating philosophy, the techniques used to infiltrate victims’ networks, and their future outlook on ransomware attacks.
This interview is an opportunity for healthcare organizations and cybersecurity professionals to better understand the enemy and prepare to deal with these threats more effectively. Knowledge is power, and we hope this information can help strengthen defenses against one of the most pressing threats of our time.
1 – RHC: Thank you guys for accepting this interview. You are a group that recently appeared in the underground, can you tell us about how and when the group Ransomcortex was born and why the choice of this name?
Ransomcortex: Ransomcortex was created in 2024, but our activities had been going on independently for a few years already.
2 – RHC: Are you a rebrand of an existing ransomware group or affiliates of other RaaS that wanted to set up on your own? Can you tell us about your motivations for opening this new ransomware group?
Ransomcortex: We have members from other groups and some members who were part of Qiulong, which shut down its ransomware operations to focus on industrial espionage.
3 – RHC: Are you currently working alone or do you already have affiliates since you recently opened? If yes, can you describe how this model works and what are the requirements to become an affiliate?
Ransomcortex: We work alone; we do not currently accept affiliates to preserve the security of our operations.
4 – RHC: Do you have specific rules that you have given yourself, such as not hitting certain areas like the CIS? Can you tell us about that?
Ransomcortex: We do not attack CIS countries, Iran, North Korea and China. Another established rule is not to attack police departments. The rest is all allowed.
5 – RHC: Since you are positioning yourself as a group working on specific targets (4 out of 4 victims are hospitals to date on the DLS), can you explain why you are focusing on health facilities? Are you also targeting regular businesses?
Ransomcortex: Our main target is the healthcare sector because it contains the most sensitive and critical data compared to other common non-government sectors.
6 – RHC: You have written in the “Advertising (Bounty $/ Work with us!)” section of your site “We offer bounties (U$D) to those who can provide physical assistance to help companies make payments in major cities. You must have your own team for physical action as well as stalkers, osinters and ‘swatters’. Your method is not important to us. Only the money is.” Can you tell us more about what this request consists of?
Ransomcortex: This is a way to outsource tasks and give an opportunity for criminals in other sectors to profit from ransomware operations, not just us, who are behind a screen.
7 – RHC: The healthcare sector has jumped to fourth place among the sectors most affected by ransomware. What monetization strategies do you employ for healthcare data in case a healthcare company does not pay the ransom? For example, resorting to private auctions or sales to pharmaceutical companies? Can you explain how this process also works in relation to the previous point?
Ransomcortex: The healthcare sector is highly monetizable because the target of extortion will never be just the victim company (if it does not pay): it is possible to extort patients for non-disclosure of their intimate health data, as well as sell the data on the black market. So an attack in this area can provide +3 monetizable sources. This is just a guess in case the company does not pay the ransom. If they pay, we will leave their patients and their data alone.
8 – RHC: Since side effects have already started as a result of ransomware attacks on hospitals-for example, in 2019 a baby was stillborn in Alabama or in 2020 a woman died in Düsseldorf due to a ransomware incident. What rules have you set for yourself so that the operation of some strategic areas of hospitals can continue to operate such as emergency rooms and not create risks for people?
Ransomcortex: In this case, the system is not encrypted. It is just data exfiltration = extortion not to disclose the data and to avoid public destruction of this company’s image.
9 – RHC: Can you explain your victim selection process? What factors do you primarily consider?
Ransomcortex: Private healthcare companies that speak English, Italian, Spanish, and Portuguese.
10 – RHC: The healthcare sector is particularly vulnerable to ransomware attacks around the world. What are the main techniques you use to penetrate the defenses of these organizations? Is there a common factor present?
Ransomcortex: We exploit some vulnerabilities, but within our team we have our own center focused on gathering information for access: OSINT specialists, social engineers, and pentesters.
11 – RHC: If you had to tell a hospital where to start to restore its cybersecurity, what advice would you give?
Ransomcortex: Raise the intellectual level of the human beings working in this hospital. Human beings are the easiest to exploit.
12 – RHC: Let’s now talk about your solution. How does your ransomware differ from other ransomware such as the popular LockBit 3.0 or Akira? If you had to explain to a potential affiliate why to start a partnership with you, what would you say from a technical point of view regarding your solution?
Ransomcortex: We do not provide RaaS. The encryption software we use is third-party.
13 – RHC: Can you describe the type of encryption used by your ransomware? What encryption algorithms do you employ and how do you ensure that victim files remain inaccessible without the decryption key?
Ransomcortex: We do not provide RaaS. The encryption software we use is third-party.
14 – RHC: Your ransomware code, does it start from known ransomware (such as the Conti code leak), or did you write it all yourself?
Ransomcortex: Before we used third-party encryption software, we had our own version rebuilt from the Conti leak.
15 – RHC: Now let’s talk about victim access points. Do you have a department that does this or do you rely on Initial Access Brokers?
Ransomcortex: Yes, we have our own department of brokers and social engineers.
16 – RHC: Do you generally operate through phishing techniques and injection of specific loaders, or do you work using specific security holes or misconfigurations (e.g. Remote code Execution or trivial passwords on RDP)?
Ransomcortex: I prefer not to answer that. But we do use some vulnerabilities and we have good phishers working with us.
17 – RHC: What kind of support do you provide to your affiliates? Do you have a dedicated team that assists them during operations?
Ransomcortex: All operations are carried out in union. For this reason, we do not intend to hire affiliates, to maintain the security and agility of operations.
18 – RHC: How do you ensure your security and anonymity in operations?
Ransomcortex: Opsec involves constant and daily analysis and reformulation, always looking for best practices. Rule number one is never rest and never think you are 100 percent secure. Paranoia must be the fuel, driving you to always strive to remain as stealthy as possible.
19 – RHC: In the case of hospital victims. Do you have a specific policy regarding the handling of sensitive patient information? For example, what happens to the data once the ransom is paid?
Ransomcortex: When the ransom is paid, the data is deleted.
20 – RHC: Have you ever had to deal with victims who could not pay the ransom? If so, since these are hospitals that can put patients’ lives at risk, how do you deal with them?
Ransomcortex: This is a good question because it brings us to the point: If hospitals don’t handle sensitive information with care, why should we? But the truth is that we keep this data safe unless our patience is tested by the company. Let me give an example: In operation qiulong, we hacked dozens of plastic surgery clinics, and 95% of these clinics kept photos of Naked patients, completely undressed, in folders on the desktop. Don’t you agree that a company that “takes care” of sensitive data in this way is not as criminal as we are?
21 – RHC: What is your long-term vision for Ransomcortex? Do you have plans to expand to other industries or geographic regions?
Ransomcortex: In the long term we will expand into new countries, so pay the ransom, because we won’t even spare the CEO’s family.
22 – RHC: Finally, is there anything you would like to say to our readers, particularly potential victims of your operations? Or any advice to healthcare providers?
Ransomcortex: The healthcare sector is the most critical and requires the utmost responsibility from healthcare administrators and entrepreneurs. Laws such as the GDPR and LGPD (Brazil) force this sector to follow a strict set of data protection guidelines, and non-compliance can result in multimillion-dollar government lawsuits and even closure of operations. But what happens in real life, especially in South America? Ninety percent of health care companies fail to comply with data protection laws and, even worse, are not punished by local governments-because governments are weak in everything, especially when it comes to enforcement against these entrepreneurs. While these companies have suffered for our crime, THEY HAVE COMMITTED TENS MORE: our only difference is that, thanks to their money (ransom), we will keep their image clean while we tarnish ours.