Frontier AI for Defenders: CrowdStrike and OpenAI TAC
CrowdStrike has been selected for OpenAI’sTrusted Access for Cyber (TAC) program. Today, OpenAI releasedGPT-5.4-Cyber, a frontier model designed for defensive cybersecurity, and expanded the TAC progr...
AI and Security: Is the Mythos Model a Breakthrough or Just Hype? Marcus Hutchins’s Vision
With the boom in artificial intelligence, bold claims about breakthroughs in cybersecurity are becoming increasingly common, but not all experts are willing to accept them at face value. A new controv...
Harvest Now, Decrypt Later: risks to your data in the near future
The Harvest Now, Decrypt Later (HNDL) model describes an attack strategy where encrypted data is collected today – despite being indecipherable – to decrypt in future when powerful quantum computers a...
From CVSS 9.8 to 7.0: What Happened to the Telegram Bug?
Yesterday, a critical vulnerability affecting the Telegram messenger was reported in the registry of the Zero Day Initiative (ZDI), identified as ZDI-CAN-30207. The issue was discovered by Michael DeP...
Just one Telegram sticker can hack you: the critical 9.8 RCE vulnerability still has no patch
There is something deeply unsettling about this vulnerability: no click is required, nothing needs to be opened. Simply receiving the content is enough. Researchers from the Trend Micro Zero Day Initi...
The Click War: Pornhub and the Global Standoff Over Age Verification
The digital landscape is undergoing a radical transformation, pitting adult industry titans against national regulators. At the heart of this dispute is not the content itself, but the gateway to it. ...
Xi Jinping and the Chinese APT’s Ambition
The post-COVID macro political movements, including ongoing conflicts, have prompted a majority of states to shift their medium- to long-term political objectives. Clearly, a paradigm shift has been v...
State-Sponsored “ILovePoop” Toolkit Targets Global Giants via React2Shell Vulnerability
The shelf life of a critical vulnerability is often measured in days, but React2Shell is proving to have a terrifyingly long tail. Months after its initial discovery, the flaw residing in React’s serv...
2149 BREAK THE SPHERE! The RHC & Hack The Box CTF at the RHC Conference 2026
In 2149, the world is no longer divided into nations, but into mega Autonomous City-States, hyper-technological urban giants competing for resources, data, and geopolitical power while the entire worl...
RHC Interviews Anubis Ransomware: Their View on RAMP, LockBit and the RaaS “Market”
Author: Luca Stivali, Raffaela Crisci, Lorenzo Nardi During the preliminary exchange leading up to the interview, Anubis expressed a very clear position regarding the collapse of several historical pl...
Latest news
The Virginia Department of Elections database may have been hacked and is online on the dark web
Identified a POC for the CVE-2024-34102 Vulnerability in Magento / Adobe Commerce
Cyberpunk 2077: Source Code Stolen?
Alleged Leak of the 2020 Israeli Voter Database
TeamViewer: Irregularity Detected in Internal IT Environment
RansomHub criminal hackers claim cyber attack on Coca Cola
Threat Actor “DragonForce” Seeks New Partners
Cyber catastrophe in sight? The new Bug on MOVEit has an Online PoC Exploit
UNZIPPED DATA – LEVI STRAUSS COMPROMISED ACCOUNTS
LockBit: The Bluff of Double Extortion Against the Federal Reserve
Xehook Stealer: The Rise and Sale of a Formidable Stealer Malware
WordPress: Five Plugins Found with Malicious Code
Alleged Data Breach of the United States Department of Defense and National Security Agency
Pietro Melillo - July 11th, 2024
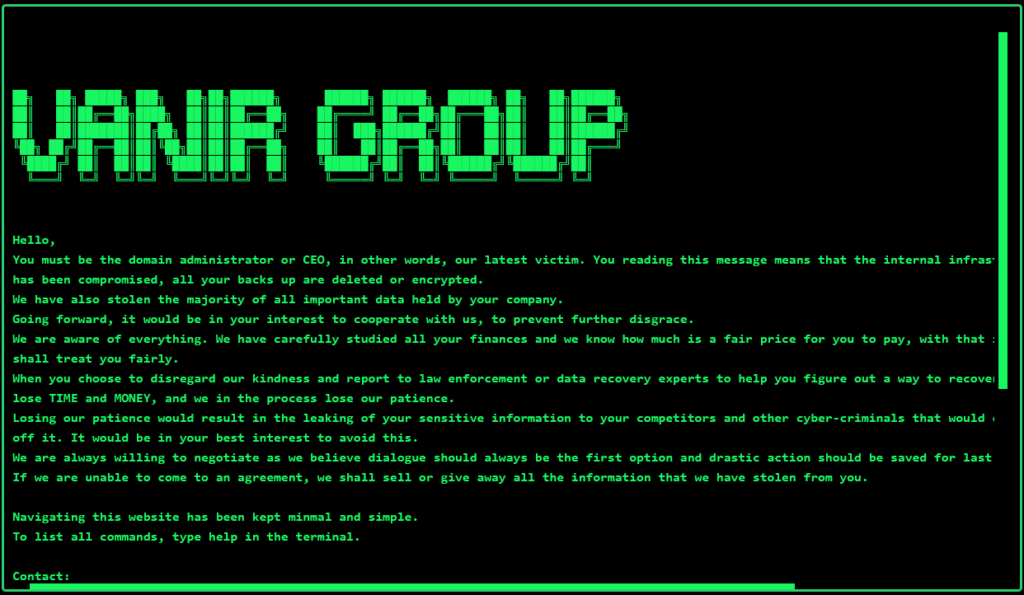
New Ransomware Group “Vanir Group”: Three Victims Immediately in Their Data Leak Site
Pietro Melillo - July 10th, 2024
The Threat Actor 888 claims responsibility for a breach at Nokia.
Pietro Melillo - July 10th, 2024
Alleged NATO Data BreachAlleged NATO Data Breach: 643 CSV Files with User Data and Server Details Leaked
Pietro Melillo - July 8th, 2024
Access to UK Accounting System for Sale: 600 Clients and 1TB of Data at Risk
Pietro Melillo - July 8th, 2024
China: 7.5 Million Tourist Data Stolen!
Pietro Melillo - July 8th, 2024
Latvian Government Database Compromised: Over 1.6 Million Government Data Lines!
Pietro Melillo - July 8th, 2024
Threat Actors Steal 5.90 GB of Sensitive Data from the Fiscalía General del Estado de Veracruz!
Pietro Melillo - July 8th, 2024
Dangerous 0day Windows LPE Vulnerability for Sale in the Underground
Pietro Melillo - July 7th, 2024
Europol Breached: Secret Documents for Sale on the Dark Web
Pietro Melillo - July 7th, 2024
Discover the latest critical CVEs issued and stay updated on the most recent vulnerabilities. Or search for a specific CVE